Data Migration Best Practices for 2024
As we move forward through 2024, the landscape of data migration has transformed dramatically, reflecting the rapid advancement of technology and the exponential growth of data. Today, organizations are compelled to migrate data not just for modernization, but as a strategic move towards efficiency, and innovation. The journey to this point has been marked by learning from past challenges, adopting new technologies, and refining strategies to ensure seamless, secure, and effective data migration. This blog post will outline essential migration best practices, focusing on planning, detailed risk assessment, and the adoption of cutting-edge technologies. These practices underscore the importance of understanding your data landscape and ensuring compatibility between source and target systems, Moreover, we will dive into the latest future trends in data migration in 2024.
8 Data Migration Best Practices
While there is no universal consensus on the migration best practices, most top technology companies agree on several top priorities. These practices are not just advice and tips but can serve as a guide and blueprint for companies before, during and after migration.
1. Create a methodology
Adopting an efficient methodology is crucial for the success of any data migration project. A striking statistic from a Bloor report highlights that 38% of data migration projects exceed their allocated time or budget, underscoring the challenges inherent in these endeavors.
Among the methodologies available, the Practical Data Migration (PDM) approach, developed by industry veteran Johnny Morris, stands out. This methodology not only offers a structured process but also includes training and certification, providing a comprehensive framework for managing migration projects.
Another methodology is: the Information Asset Inventory (IAI), this approach is a systematic method used by organizations to identify, classify, and manage their information assets effectively. This process is critical for understanding the scope of an organization’s data, ensuring proper data management practices, and supporting strategic decisions regarding data security, compliance, and risk management. Here’s how it typically unfolds and why it’s essential, especially from an IT manager’s perspective:
- Identification: Cataloging all the information assets within the organization. This includes databases, files, and applications.
- Classification: Assigning a value and sensitivity level to each asset based on its importance to the business, regulatory requirements, and potential impact of compromise or loss.
- Ownership: Determining who within the organization is responsible for managing, securing, and maintaining each asset.
- Protection: Assessing current security measures and identifying any gaps in the protection of these assets to ensure they are safeguarded against threats.
2.Analyze your data migration project
Assessments serve as the critical groundwork for any data migration project. Conducting a thorough migration assessment equips organizations with a comprehensive understanding of the entire data transfer process, including the transition of data across different locations, formats, and systems. It’s essential for these assessments to pinpoint potential risks and advantages, identify the current storage locations of data or systems, and determine their migration destinations. The proposed mapping between source and destination is key to planning and executing the migration.
Furthermore, the assessment phase should clarify whether to employ an all-at-once or a phased or gradual migration strategy. It’s also the time to outline the necessary budget and timeframe, establishing a detailed project timeline early in the process.
Evaluating essential elements such as backup procedures, target systems, security measures, and support infrastructure is indispensable during a data migration assessment. Organizations must also consider possible cloud provider downtime, and be aware that sometimes the cloud service might be unavailable. While less of a concern in the cloud, any planned downtime, both in source and destination, needs to be planned for and accommodated.
“Downtime is an inevitable reality for almost every business,” said Yonatan Hatzor, co-founder and CEO of Parametrix, a company specializing in cloud downtime insurance. “As companies increasingly rely on cloud providers for day-to-day operations, they are exposed to the real risk of downtime.”
According to a report by Parametrix, the major cloud service providers, commanding over two-thirds of the global cloud market, experienced 1,190 performance interruptions in their cloud infrastructure in 2022. Out of these, 492 disruptions were deemed critical. The report also highlights that approximately one-third of these incidents affected cloud regions in the United States, with the remaining critical disruptions distributed fairly evenly across Europe, Asia, and other parts of the world.
3.Engage stakeholders outside of the IT department
Engaging with stakeholders beyond the IT department is crucial when initiating the planning and design phases of a migration project. It’s essential to inform all employees about the potential impact of the migration on their daily tasks and to offer them a chance to share their input.
Frequently, staff members from departments other than IT play a pivotal role in the migration effort. Their insights into the practical usage of data assets and systems in their daily operations, as well as their expectations for improvements following the migration, can significantly inform and enhance the migration strategy.
4.Test in-depth in a controlled environment
When exploring the capabilities of a new system, it’s crucial to ask its providers if they offer tools that can enhance user confidence through repeatable and user-friendly testing mechanisms. Inquire whether any new system providers offer tools designed to bolster user confidence, such as the ability to conduct repeatable system tests. Ideally, these tests should be streamlined to minimize the need for expert users to enter extensive details, facilitating ease of use and efficiency in evaluating the system’s reliability and performance.
5.Backup your valuable data before the migration process
Throughout the migration process, it’s imperative that the original source data or system remains unaltered, regardless of any significant data issues that may arise. To safeguard against any potential damage, alterations, or corruption, companies must perform comprehensive backups to guarantee the availability of reliable data copies when necessary.
The primary risk associated with data migration lies in the potential loss of business-critical assets or the improper handling of sensitive data. By maintaining data backups on distinct and highly secure systems, companies can effectively mitigate the risks of errors or data loss during the migration.
Cloudsfer’s cloud-to-cloud backup solution stands out in this context, offering a robust safety net by creating reliable and secure copies of data across different cloud platforms. Such backups are essential, especially considering the high stakes of losing business-critical assets or mishandling sensitive data during migration. Cloudsfer’s solution provides an additional layer of security, enabling companies to navigate the complexities of data migration with confidence, knowing they have a dependable recovery option in the event of any unforeseen errors or data loss.
6.Prioritize security throughout the process
Data encryption is a critical component of data migration, serving as a cornerstone for ensuring the security and integrity of data as it moves from one system to another. When data is encrypted, it’s converted into a secure code that can only be accessed or decrypted by users with the correct encryption key. This process safeguards sensitive information from unauthorized access, data breaches, and other cyber threats, especially during the vulnerable phases of transmission and storage in new environments.
In the context of data migration, encryption plays a dual role. First, it protects data in transit between the old and new systems, ensuring that any data intercepted during the migration remains unreadable and secure. Second, encryption secures data at rest within the new system, preventing unauthorized access even after the migration is complete.
In Tzunami Deployer, the data migration process to SharePoint Online, utilizing the Microsoft 365 migration API, is securely encrypted end-to-end. This ensures that from the moment data leaves the original source until it is safely stored in SharePoint Online, it remains protected and inaccessible to unauthorized parties. Tzunami Deployer emphasizes customer data privacy and security, asserting that it does not access or process customer data directly. The solution operates offline, behind the company firewall. Minimizing the risk of data exposure and enhancing the security posture of the migration process. This approach underlines Tzunami Deployer’s commitment to maintaining the integrity and confidentiality of customer data throughout the migration journey.
7.Test your migration continuously
Organizing your migration into distinct phases is advisable. Migrating to the cloud typically takes time according to the volume of the data to migrate. However, for larger organizations dealing with vast amounts of data and complex systems, this timeline can extend further. By segmenting the migration into smaller, manageable stages, you can more effectively monitor progress and identify any obstacles early on. Conducting live testing at each stage of the migration is beneficial. These tests provide a practical way to verify your initial assessments and plans against the realities of the migration process and to evaluate the performance of systems once they have been migrated. Additionally, these tests offer the opportunity to refine your migration strategy in real time, ensuring a more controlled and efficient process.
Tzunami provides extensive, detailed migration reports during the export, deployment, and migration processes, enabling users to ensure all content is successfully migrated.
8.Migration optimization is necessary
Migration optimization directly contributes to the efficiency and effectiveness of your applications and services, which may be at the heart of your customer’s experience with your brand. From an operational perspective, you can achieve better performance, cost savings, and improved resilience by fine-tuning your cloud infrastructure post-migration. It also helps mitigate any potential data loss or downtime risks.
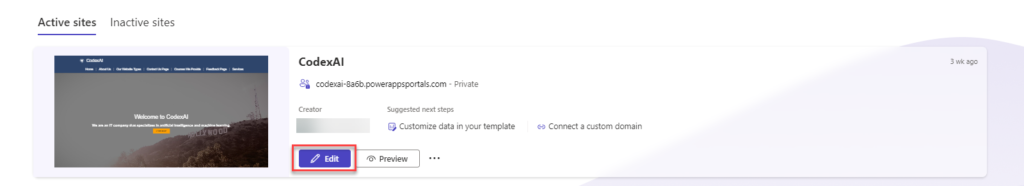
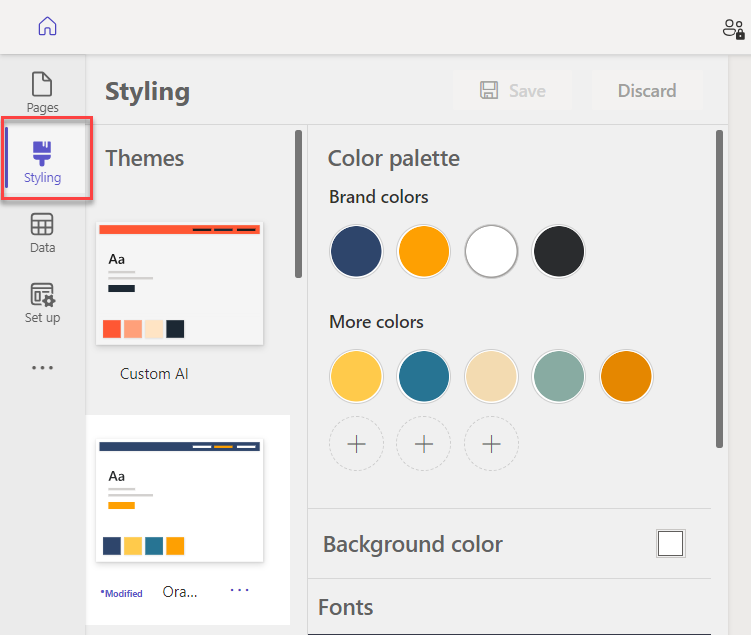
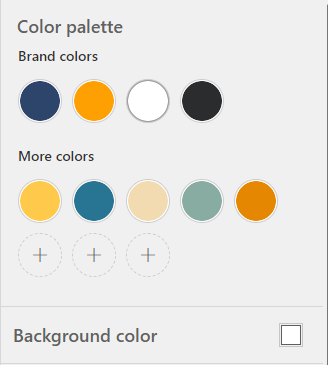
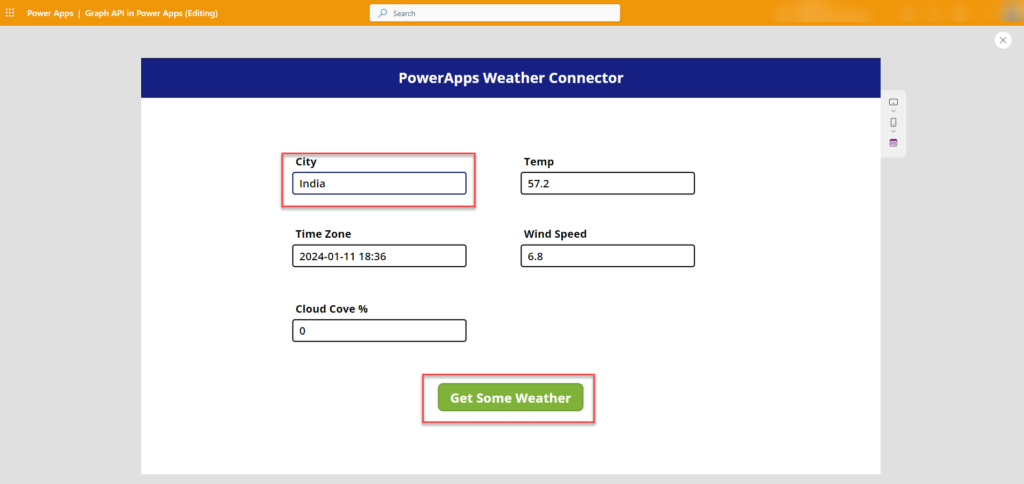
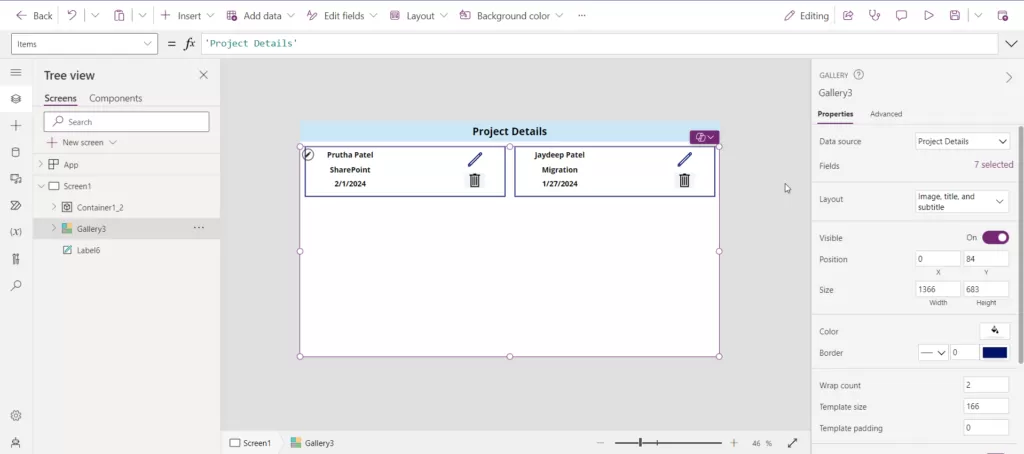
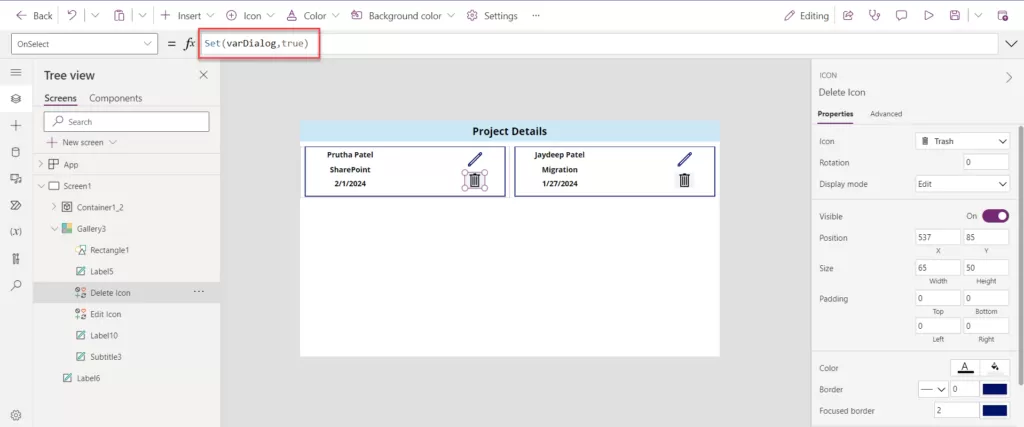
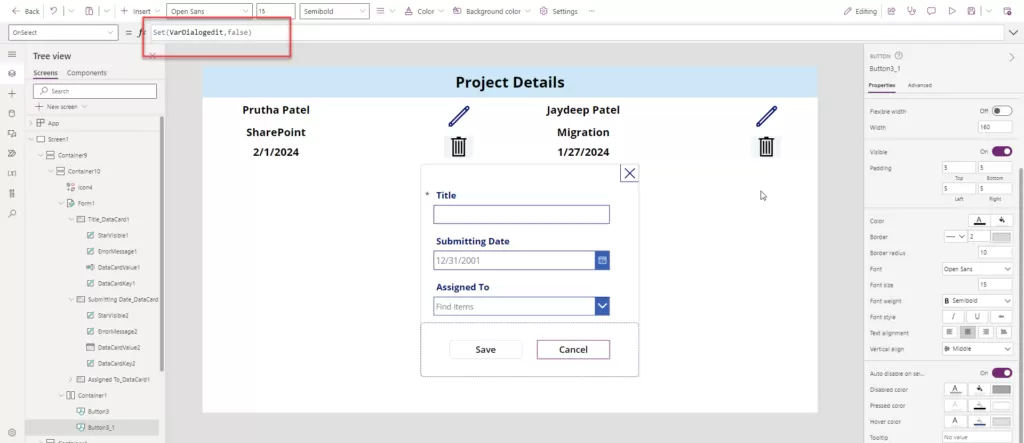
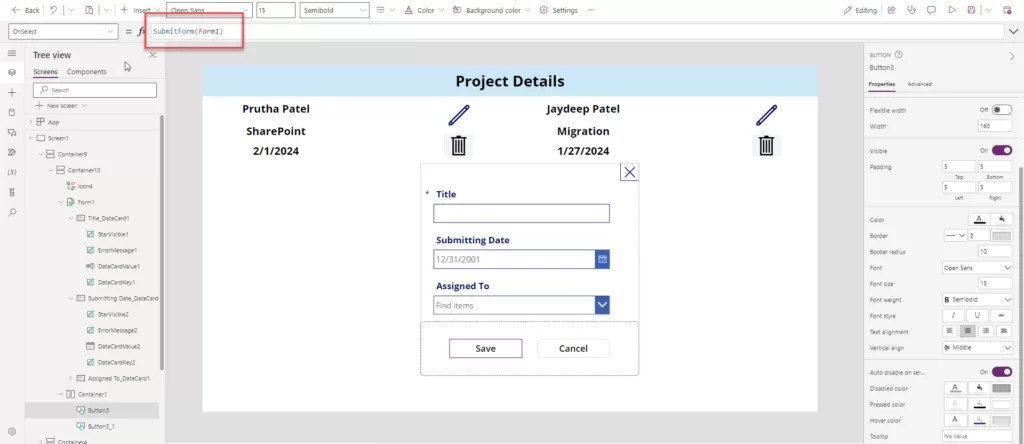
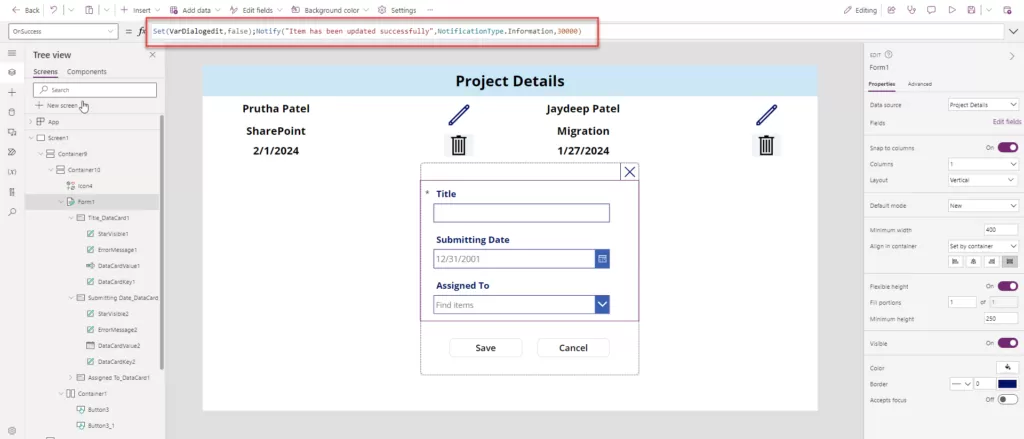
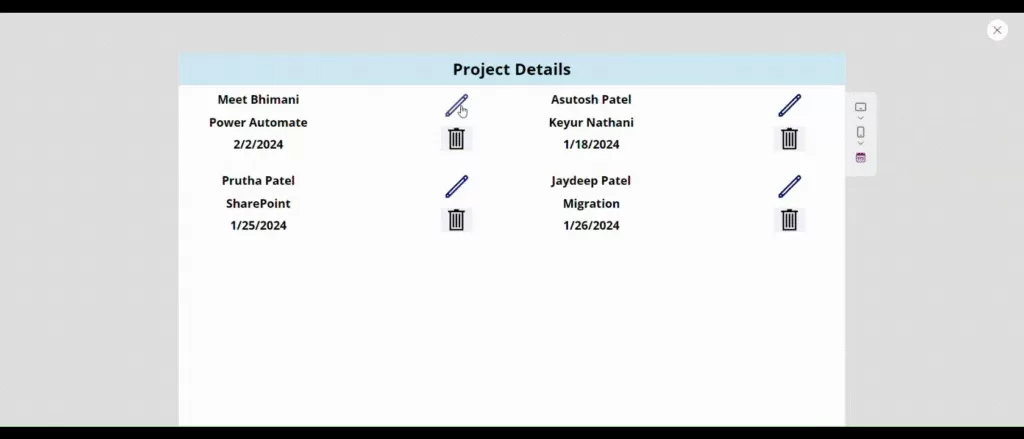
After migrating your data to SharePoint with the Tzunami migration tool, you can optimize your SharePoint environment with Reality Tech. As an award-winning provider, Reality Tech excels in SharePoint deployments, upgrades, workflows, and custom solutions. By focusing on core business operations and enhancing collaborative workflows, Reality Tech leverages its deep understanding of the business landscape to deliver solutions that significantly enhance efficiency, speed, and agility.
Deep dive into data migration trends for 2024
Data migration continues to be a critical process for businesses of all sizes. In 2024, we can expect to see some exciting trends emerge that will shape how organizations move their data between systems. Here’s a closer look at three key areas:
1.Cloud Migration Takes Center Stage:
Businesses are rapidly embracing the cloud for its scalability, cost-efficiency, and flexibility. This naturally translates to a surge in data migration projects by 2024. Organizations will move data from on-premises storage to cloud platforms like SharePoint migration to the cloud, Office 365, Autodesk Construction Cloud (ACC), and migrate file server AWS, or Azure to unlock these benefits. Hybrid and multi-cloud strategies will also gain traction, requiring robust tools to handle complex data movement across diverse environments.
2.Automation: The Efficiency Engine:
Manual data migrations are cumbersome and error-prone. To address this, 2024 will see a rise in automation tools that streamline the process. These tools can automate tedious tasks like data extraction, transformation, loading, and validation.
3.Security: A Constant Vigil:
Security remains paramount even with the ease of cloud migration and automation. Organizations will be laser-focused on data privacy and compliance throughout the process. This includes robust encryption, access controls, and leveraging data residency options offered by cloud providers. Microsoft and SharePoint Online are at the forefront of the market in terms of data security, offering robust protection measures that meet the needs of today’s digital landscape
In conclusion, the evolution of data migration strategies in 2024 has underscored the critical importance of planning, comprehensive risk assessment, and the integration of advanced technologies. Through adopting methodologies like Practical Data Migration and Information Asset Inventory, organizations have enhanced their ability to manage complex data landscapes efficiently. As we move forward, these best practices not only serve as a foundation for successful data migration projects but also as a testament to the ever-evolving nature of technology and its role in shaping the future of business operations.